It used to be that state-sponsored cyberweapons were reserved for targeting dissidents, diplomats, and high-value political targets. Not anymore. In a terrifying escalation of the mobile security landscape, Google’s Threat Analysis Group (TAG) has uncovered a sophisticated iPhone crypto scam kit being used to drain ordinary wallets.
The malware, dubbed ‘Coruna,’ marks a dangerous shift: tools originally designed for espionage are now being deployed to steal your private keys.
Lunaray Security Alert
Google threat researchers have discovered a new exploit toolkit called #Coruna for Apple iPhones that can steal mnemonic phrases from cryptocurrency wallets, affecting devices running iOS versions 13.0 to 17.2.1.
Please stay vigilant!
— Lunaray (@lunaray_co) March 5, 2026
DISCOVER: Secure your assets with our guide to the Best Bitcoin Desktop Wallets
iPhone Crypto Scam: How the Coruna Malware Works
Most crypto scams rely on you making a mistake like clicking a bad link or signing a malicious transaction. The Coruna malware, a crypto scam that affects iPhone running on older software versions, is different because it doesn’t need your permission to enter. Google TAG report explains how this exploit kit is embedded in fake websites that mimic legitimate services, such as the crypto exchange WEEX.
When a user visits one of these compromised sites using a vulnerable iPhone (running iOS versions 13.0 through 17.2.1), the kit silently fingerprints the device. If the software is outdated, it deploys a sophisticated exploit chain to gain deep access to the phone’s system.
Once inside, the malware doesn’t just sit there. It actively hunts. It scans your device for specific apps like MetaMask, BitKeep, and Phantom. It searches your photos and notes for keywords like “backup phrase,” “seed,” or “bank account.” The goal is a silent crypto wallet hack: exfiltrating your recovery keys to a remote server before you even realize your funds are at risk.
DISCOVER: Next Possible 1000x Crypto in 2026
From Spies to Scammers: A Dangerous Pattern
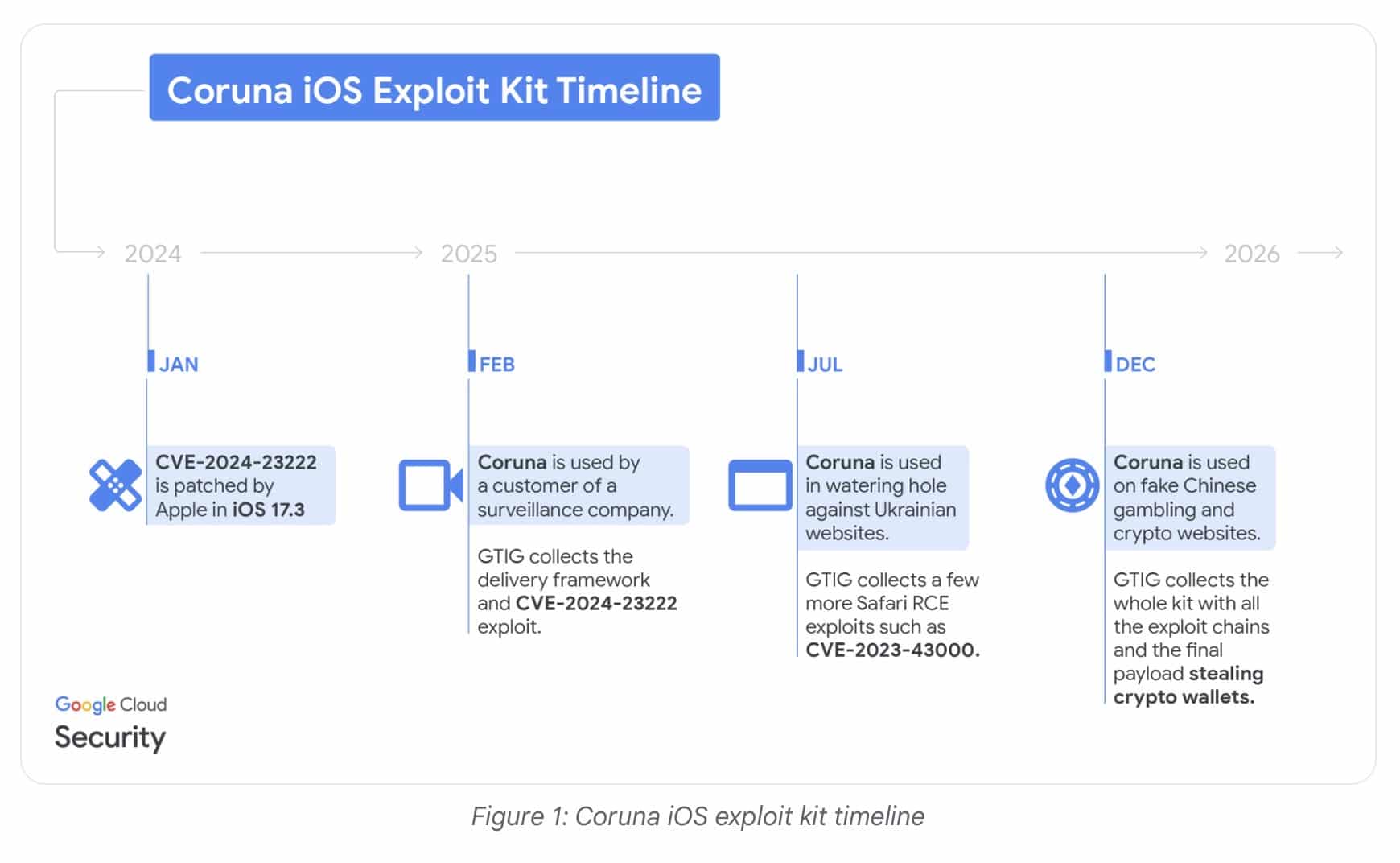
This development confirms a trend we have been warning about for years: advanced cyber tools eventually trickle down from governments to criminals. Google TAG researchers traced the origins of Coruna back to commercial surveillance vendors in early 2025. It was later spotted being used by suspected Russian espionage groups targeting Ukraine. Now, it has landed in the hands of financially motivated crypto thieves.
This is the digital equivalent of military-grade hardware being sold on the black market to street gangs. We are watching a rapid commoditization of zero-day exploits. Just as we have tracked recent cases of organized crypto scam rings expanding their operations, the arrival of Coruna shows that these groups are no longer relying solely on social engineering. They are purchasing or repurposing tools that can bypass operating system security entirely.
Organized crime groups are now operating with the technical sophistication previously reserved for nation-states, looking to harvest private data at scale.
DISCOVER: 5 High-Risk High-Reward Cryptos
Who Is at Risk and How to Know If You Are
If you are using an iPhone aimed at trading or storing crypto, you need to pay attention to your iOS security settings immediately. The Coruna exploit specifically targets devices running iOS versions older than 17.2.1. First thing you can do: check if your iPhone is update to the latest version.
The scary part of this exploit is the silence. Unlike a phishing email, where you might spot a typo, this attack happens in the background. If you have visited shady gambling sites, aggressive pop-up exchange offers, or untrusted crypto news aggregators recently, your device could have been fingerprinted.
This highlights the critical importance of how you manage your private keys. As discussed in relation to future-proof security architectures, relying solely on a mobile phone’s software wallet, especially on an outdated operating system, is becoming increasingly negligent.
If your seed phrase is stored in a screenshot in your Photos app or typed into your Notes app, Coruna can find it, encrypt it, and ship it to the attackers.
DISCOVER: The Best Hardware Wallets to Keep Your Crypto Offline
Follow 99Bitcoins on X For the Latest Market Updates and Subscribe on YouTube For Daily Expert Market Analysis.
The post iPhone Crypto Scam? Google Warns of Nation-State Wallet Drainer appeared first on 99Bitcoins.
#iPhone #Crypto #Scam #Google #Warns #NationState #Wallet #Drainer
#iPhone #Crypto #Scam #Google #Warns #NationState #Wallet #Drainer